When you think about cybersecurity, you probably picture antivirus software, password protectors and multifactor authentication.
All of these things are important, but they’re not as important as correct employee training.
Each of your employees has the power to accidentally make your business vulnerable through one mistake. So you need to ask yourself, how cyber-aware is your team and how long before an accidental breach impacts your business?
Read on to learn the top 8 ways human error is putting your cybersecurity at risk.
What is Human Error in Cybersecurity?
Human error in cybersecurity refers to the mistakes people make that can lead to data breaches or their security being compromised.
For example, an employee may fail to update software, be tricked by a phishing attack, or click a suspicious link. Human error can lead to catastrophic consequences like financial losses and reputational damage, especially for small businesses.
How Common are Human Error Breaches?
Deloitte recently released their Future of Cyber 2023 report which revealed some startling cybersecurity statistics.
They found that 95% of all cybersecurity events involved some degree of human error. This can range from sharing sensitive information on public networks to clicking on a suspicious link.
While 95% is a scary number, it also means by professionally training your team to avoid human error breaches, you could make your business 95% safer!
The Top 8 Ways Human Error is Putting Your Cybersecurity at Risk
1. Phishing Scams
Phishing scams are when a hacker tries to manipulate you or one of your employees using social engineering. In this case, they use fake emails, SMS messages, phone calls etc to trick you into giving them access, information or money.
While you might think you’d never give a stranger your details, phishing scammers are smart and will disguise themselves as people you trust, like friends, your workplace or institutions like your bank.
With the emergence of sophisticated AI software that can help them write convincingly, can alter voices and create images, phishing attacks will become more deceptive in the future, so you need to be wary.
2. Vulnerable Passwords
If you use the same password for everything, that’s bad. If your employees also use the same password, or worse, share a common password, that’s even worse.
Having the same password for everything means a cybercriminal only needs to breach one of your accounts to have access to all of them.
Using simple or common passwords also leaves you vulnerable. People often use passwords that are easy to remember, like their name or birth date, “1234” or “password.” The problem is, these kinds of passwords are also really easy for hackers to guess.
Using strong, unique passwords and changing them regularly is important if you want to prevent data breaches. Just remember, when you’re part of a business it isn’t just your password that needs to be strong, it’s the passwords of all your team members as well.

3. Sharing Sensitive Information
No matter how well you protect your business information with systems, poorly trained employees can still unwittingly share sensitive information.
Details like passwords or financial information can be shared through unsecure channels. For example, an employee with a compromised mobile device might message a password to their colleague, and this password will be intercepted by a hacker.
These seemingly small acts of defying cybersecurity best practice can have devastating consequences for your business, so it’s vital you make sure your team is well-trained.
4. Out-of-Date Software
All your work devices should be set to automatically update, but if your employees sometimes use personal devices for work, they may have out-of-date software.
Outdated software can leave systems vulnerable to cyberattacks. Hackers exploit known vulnerabilities in software that hasn’t been updated. This is such a common form of attack that cybercriminals have forums to discuss and share the latest exploits.
So make sure every device used in your business, whether supplied by you or your employees, is automatically updating itself.
5. Downloading Malicious Software
Downloading malicious software, known as malware, is like giving cybercriminals direct access to your system.
Malware is usually delivered by tricking a user into accessing it, often by masquerading as an innocent source. Unfortunately, without proper training, your employees may download or click suspicious files and links.
It only takes one person to invite a cybercriminal into your systems, which could cause significant damage to your business’ financial situation and reputation. To help prevent this, limit the permissions for your employees to download and install unapproved applications.
6. Using Public Wifi
After COVID-19, work from home arrangements are commonplace. While this gives your employees flexibility, but it also takes them away from your secure workplace wifi.
Public networks are more vulnerable to being breached, where hackers can intercept the data being transferred.
While it may be tempting for your team to spend part of their work from home day in a cafe, at the very least they need to avoid using public wifi when accessing work financial accounts.
7. Physical Security
Many people forget about physical cybersecurity. While the two terms may sound like they contradict each other, with phones and tablets increasingly being used for work, the danger of a device being lost or stolen has never been higher.
Your employees need to make sure they never leave any device used for work in public places. They should also be in the habit of logging out of secure applications and locking the device when it isn’t attended.
If a device does ever go missing, it is essential that they inform you immediately so passwords can be reset and account activity can be monitored.
8. Lack of Training
By now you’re probably noticing a trend – a lack of education about cybersecurity can lead to a lot of incidents!
The reality is, data breaches occurring because of human error is one of the largest risk factors for businesses today. Employees who aren’t properly trained in cybersecurity best practices can make mistakes that lead to breaches, and as the business owner, it’s your responsibility to ensure they are trained correctly.
Providing professional cybersecurity training is the only way you can help employees identify security threats!
OneCloud IT Solutions
Even if you have a strong cybersecurity awareness, your employees might not. That’s why training your team on proper cybersecurity protocols is essential if you want to protect your business.
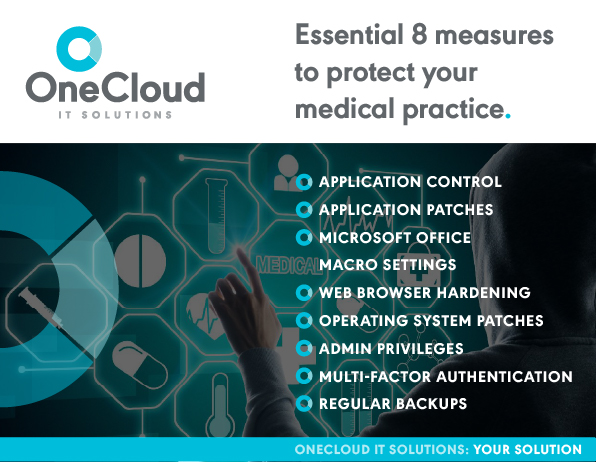
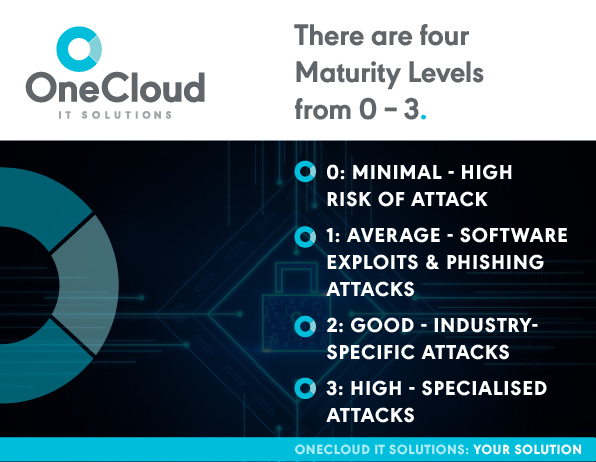
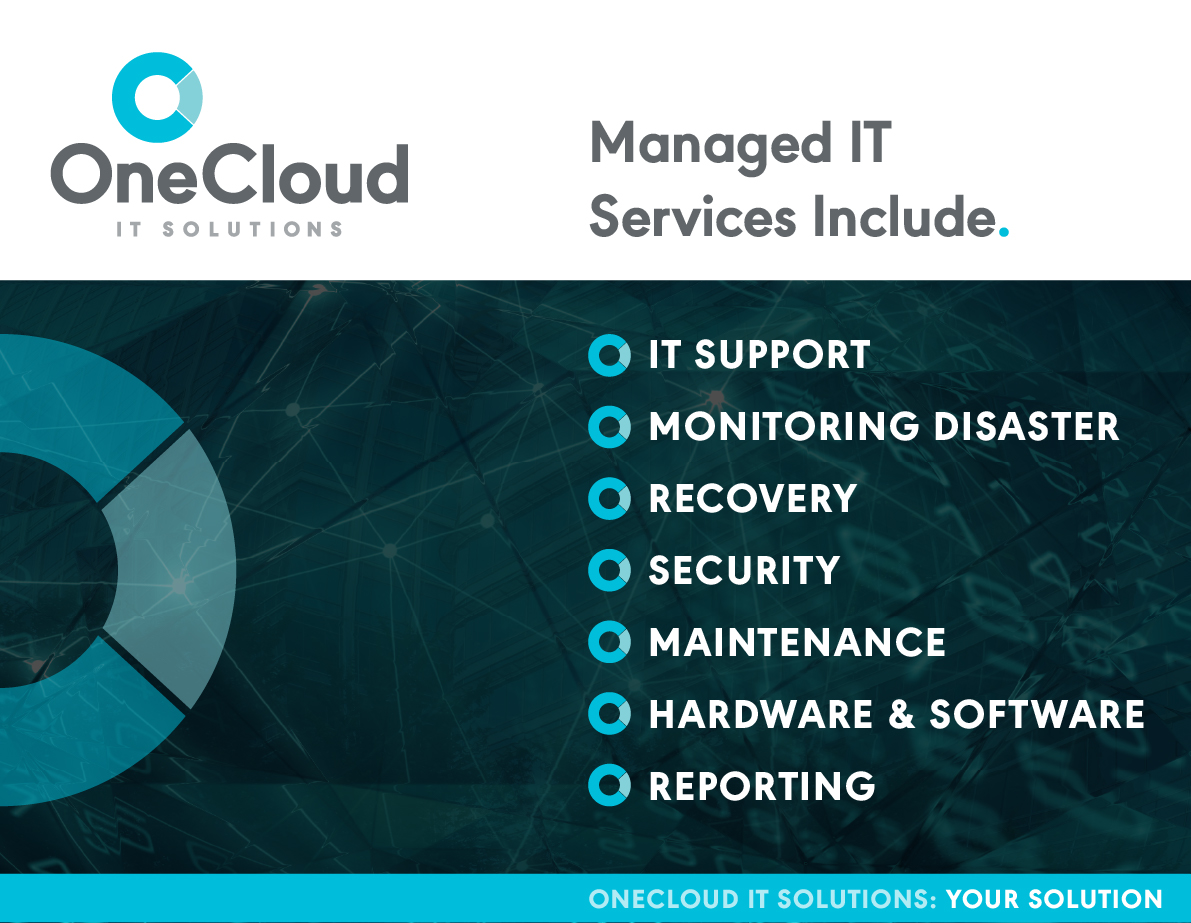
At OneCloud IT Solutions, providing cybersecurity for small businesses like yours is our speciality. Not only will we implement the Essential 8, we’ll also train your team to eliminate the risk of human error.
For more information about our service, or to book a consultation, get in touch today.